
Confidentiality is a basic pillar of data safety. In delicate deployments, resembling these involving federal governments, army and protection companies, and huge monetary establishments, the demand for confidentiality extends properly past the standard 5 to 10 years, typically reaching 20 years or extra.
The identical additionally applies to telecom operators and enterprises offering companies to any of those vital companies. With the present classical computer systems, this requirement of ahead secrecy for encryption might be met simply as breaking the uneven cryptography (deriving the non-public key for a given public key) would take properly past the timelines wanted to keep up the information confidentiality.
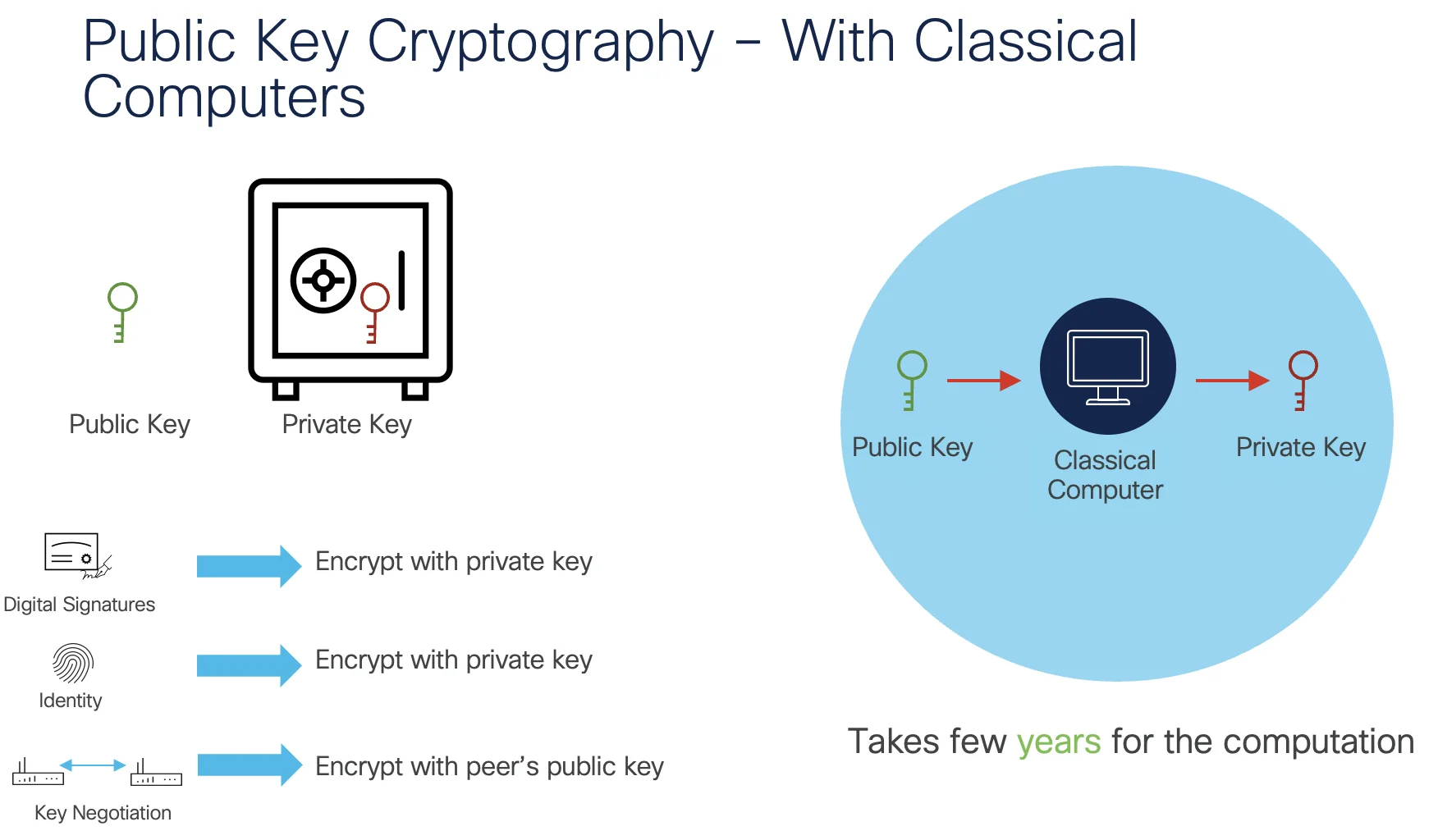
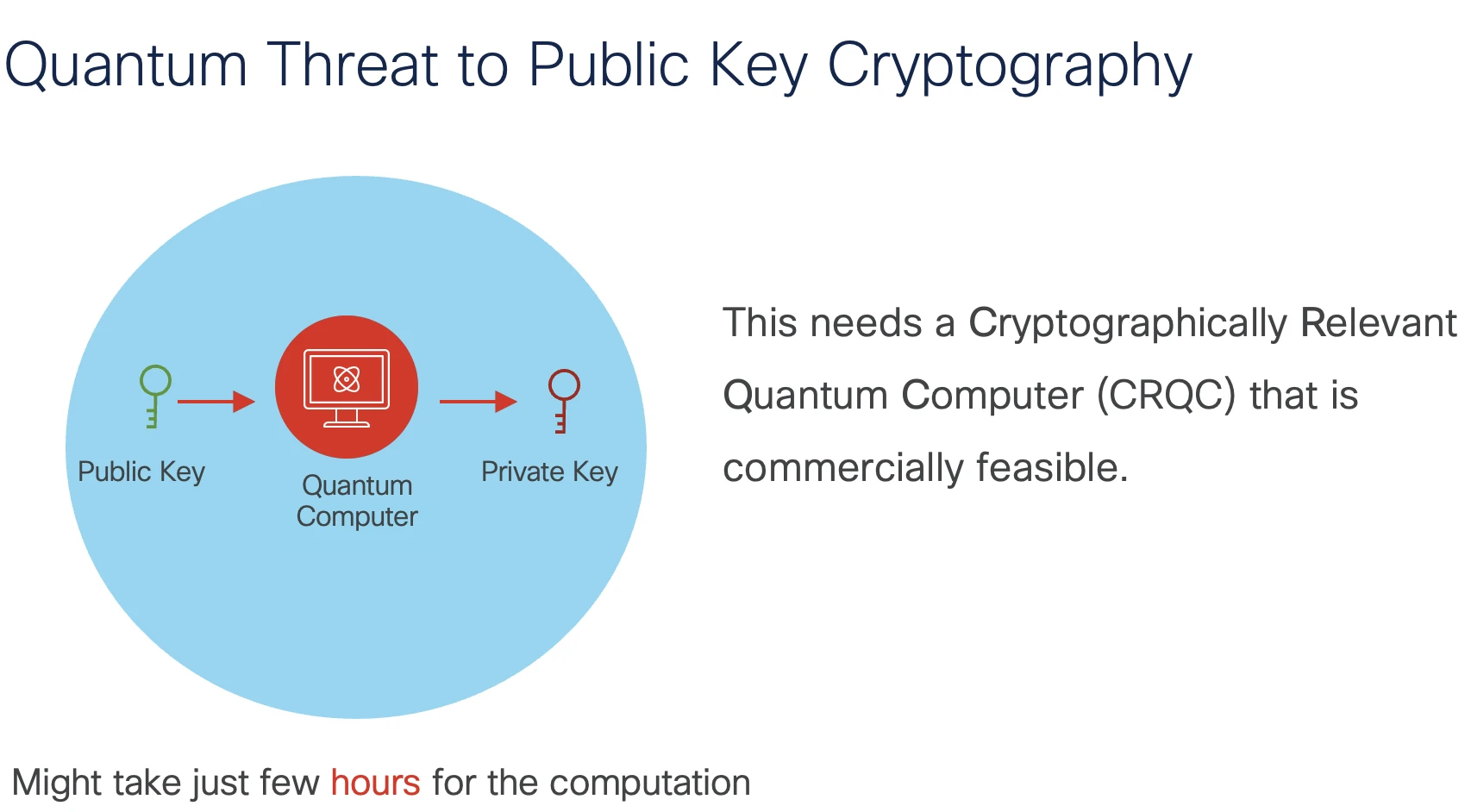
Nevertheless, it will change with the appearance of Quantum Computer systems, and particularly as soon as we have now Cryptographically Related Quantum Computer systems (CRQC) out there. The time taken to derive the non-public key for a given public key can go from a couple of years to a matter of few days or hours. This is able to imply, the ten – 20 years’ timeframe of confidentiality requirement for delicate community deployments can not be met with the present cryptographic algorithms.
Though we don’t have a sensible CRQC out there but, because of the nature of Harvest Now, Decrypt Later (HNDL) assaults the place attackers can simply faucet the delicate flows in the present day and will decrypt them later, federal / authorities companies, monetary establishments, and so on. should begin performing now to be prepared for this impending Quantum menace to encryption. The identical has been highlighted in the latest Government Order by the US authorities too.
Along with the menace to key negotiation for transport safety protocols like MACsec / IPsec, there are different elements of community safety that may be impacted with the appearance of Quantum Computer systems as listed beneath:
- Picture Signing: Digital signatures can be impacted which might imply new Quantum protected signatures have to be adopted to signal the NOS (Community Working System) and different binaries.
- Safe Boot Course of: The whole Safe boot course of should proceed to be trusted which might imply adopting Quantum protected signatures to every of the boot time artifacts.
- Runtime Integrity: As soon as the units are booted, the run time measures make sure the trusted state of the NOS like Linux IMA (Integrity Measurement Structure) should undertake Quantum protected algorithms.
- Operational Safety: All of the operational security measures counting on SSH, TLS, and so on. should undertake the newly accredited PQC algorithms.
- Guaranteeing {Hardware} Trustworthiness: Identities together with cryptographic {hardware} identities like Cisco SUDI have to undertake Quantum protected algorithms.
- Hashing: Any safety characteristic that makes use of hashing should begin supporting at the least SHA-384 or SHA-512 hashes to be Quantum Protected.
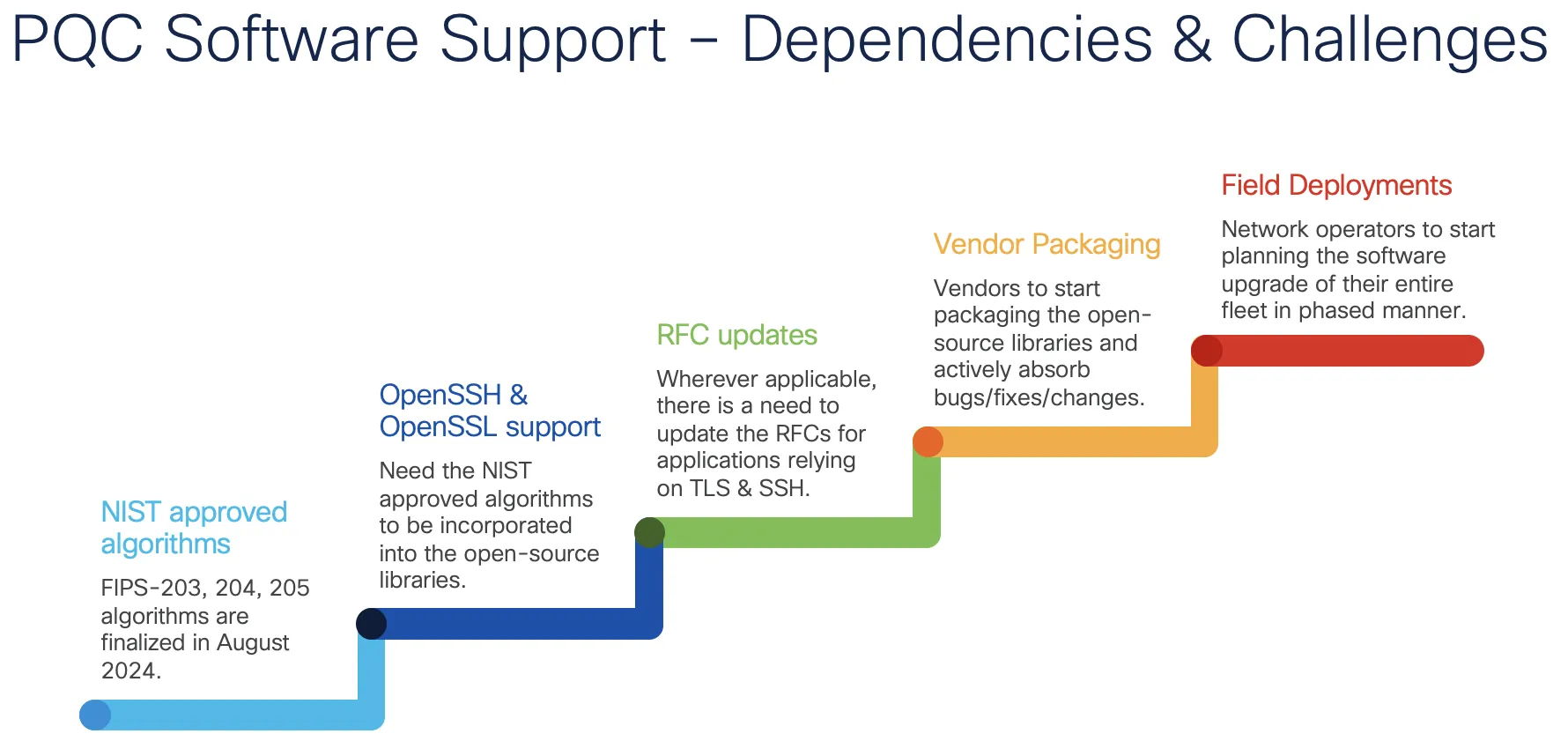
As seen above, even earlier than operators allow transport safety protocols like MACsec or IPsec, the truth that they’ve a router or a swap working of their community would imply they should begin evaluating the transition to Quantum Protected options. With such a wider scope of the menace, the transition journey should begin now given the variety of steps concerned (proven beneath) in upgrading the units to a Quantum protected resolution.
In contrast to selective upgrades of community units based mostly on what options are wanted within the area, the Quantum safety menace would require all of the units to be upgraded. The affect is far better on the subject of community units managing vital utilities which are typically deployed in distant places the place there might be operational challenges for the upgrades.
Along with this, Cisco routers help options like Chip Guard, which assist detect tampering of CPU or NPU throughout transit. That is made doable with Cisco’s Belief Anchor module (TAm) chip that’s current on each system. Cisco’s Safe Boot course of verifies if the router nonetheless has the identical CPU or NPU when it was shipped from a Cisco facility.
This sort of distinctive {hardware} integrity measure should even be made Quantum protected to keep up the identical stage of belief within the Quantum Computing period. Any new {hardware} at present in design section and anticipated to ship in CY’2027 or past, will must be within the area for an additional 10 – 15 years at the least. So, it turns into mandatory to include Quantum protected measures within the {hardware} too as there may be extra likelihood of those units being vulnerable to the Quantum Computing menace throughout their deployment timelines. That is the place community tools distributors, silicon distributors, community operators, requirements our bodies and the tip customers should come collectively now to begin planning for the transition to Quantum protected safety options.
Lastly, in my earlier weblog publish on Quantum menace to community safety, the menace to move protocol safety was highlighted together with the out there options from Cisco. To this point, the options to handle the menace to key negotiation had been centered round numerous types of Quantum Key Distribution strategies. Nevertheless, with the current publication of PQC (Publish Quantum Cryptography) algorithms by NIST, it’s time to implement these algorithms natively for key negotiation.
Cisco is actively engaged on Quantum Protected Safety options and can also be concerned in numerous requirements our bodies engaged on Quantum Protected Cryptography options. Extra particulars on this may be discovered on our Publish-Quantum Cryptography belief middle web page.
There will probably be classes from Cisco audio system on the upcoming Quantum Networks Summit on this matter. Please take a look at the agenda and be a part of us for the tutorial session together with the session on Cisco’s plans on Quantum readiness for encryption.
We’d love to listen to what you assume. Ask a Query, Remark Under, and Keep Related with Cisco Safe on social!
Cisco Safety Social Channels
Share: